AI Agent + RPA for Loan Boarding & Servicing Transfers: A Secure Implementation Blueprint (Escrow, Insurance, and Payment Histories)
2026-05-05
Set clear scope and success criteria before automating transfers
Loan boarding and servicing transfers tend to break down in predictable places: unclear scope, ambiguous ownership between prior and current servicers, and inconsistent definitions of “done.” AI agents and RPA change throughput, but they also magnify gaps in field definitions, document completeness, and reconciliation requirements. Executive alignment often becomes the binding constraint, because cycle-time gains erode quickly when auditability, exception volume, or investor reporting integrity deteriorates during high-volume boarding events.
Transfer scope and data inventory
Transfer scope frequently extends beyond loading loan records. Escrow setup, insurance status, and payment history attributes often sit across multiple sources with partial overlap and competing “systems of record.” A data inventory sets the operational boundary between elements that can be automated with stable assumptions and elements that remain conditional due to prior-servicer variability, missing documents, or inconsistent field-level ownership.
Success metrics and quality targets
Success is often framed as cycle time, accuracy, and review effort, but executive confidence typically hinges on quality targets that hold up under audit review. Trusted automation uses explicit variance thresholds, consistent routing into review, and reporting that enables portfolio-level visibility without suppressing exceptions. Dashboard-ready metrics become the shared reference point across operations, compliance, and technology leadership.
Design a secure automation approach that limits sensitive data exposure
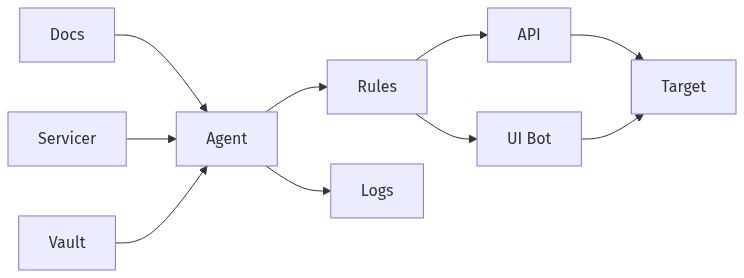 Secure connections that limit sensitive data exposure
Secure connections that limit sensitive data exposure
Security posture is often the deciding factor for production automation in servicing transfers, particularly when PII moves across document repositories, servicing platforms, and reporting layers. AI agents add orchestration and decisioning, while RPA executes against systems of record; together, they can reduce exposure through controlled handling or expand PII sprawl through overly broad access. A defensible blueprint typically emphasizes least-privilege connectivity, limits data duplication, and treats traceability as a core control rather than a secondary consideration.
Integration approach and fallbacks
API-first connectivity usually creates clearer control points and more consistent audit evidence than screen-driven automation, particularly across regulated servicing operations. UI-based fallbacks remain common where APIs are incomplete, but their fragility becomes a governance issue when screens change and automated actions become difficult to validate consistently over time.
Sensitive data handling and access hygiene
Sensitive data handling often fails through convenience patterns: broad data pulls, unnecessary replication, and shared credentials for non-human identities. Access hygiene is closely tied to GLBA safeguards and prevailing privacy expectations, since audit findings frequently map to avoidable exposure paths rather than to the automation tooling itself.
Control access and approvals for bots, agents, and reviewers
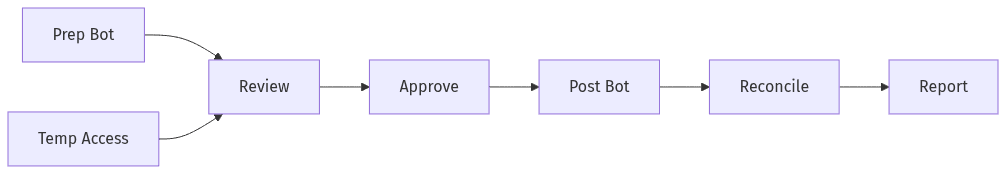 Roles and approvals across prepare, post, and reconcile
Roles and approvals across prepare, post, and reconcile
Automation in loan servicing only becomes operationally credible when accountability stays unambiguous. Role-based access control and segregation of duties limit the risk of a single automation identity preparing, posting, and reconciling changes without a defined approval boundary. From a governance perspective, the question is less whether AI agents can accelerate boarding work and more whether automated actions present as controlled operations under internal audit, regulators, and vendor risk oversight aligned with SOC 2 expectations.
Roles, permissions, and approval boundaries
Separation between preparation, approval, posting, and reconciliation reduces control ambiguity, especially for cash-impacting and investor-sensitive fields tied to escrow and payment history. Dual-control expectations commonly surface around overrides, negative amortization risk signals, or insurance status changes that can trigger force-placed outcomes or customer impact.
Temporary access and monitored exceptions
Servicing transfers create time-bound pressure that often leads to privileged exceptions, particularly during boarding windows and cutoff dates. Temporary access with monitored escalation can function as a risk valve, but it also draws audit attention when authentication strength, privileged access logging, and reviewer accountability lack consistent evidence across the life of a transfer.
Make outcomes reviewable with audit-ready records and evidence
Audit readiness in AI-driven servicing transfer automation rarely depends on model sophistication; it depends on reconstructability. Evidence trails that link inputs, extracted document values, system actions, and reconciled outputs reduce friction during internal review and external examinations. A recurring misconception treats logs as sufficient evidence, yet audits typically require durable artifacts and provenance that explain why a value changed—not merely that it changed—under policies aligned with SOC 2 and related control expectations.
Evidence capture and durable records
Evidence capture typically includes source documents or references, extracted fields, validation results, and system confirmations tied to each boarded loan. Durable records strengthen defensibility when disputes arise over payment histories, escrow balances, or insurance coverage, and they reduce rework when downstream reporting teams reconcile outcomes against investor, regulator, or customer service inquiries.
Decision traceability and reviewer signoff
Decision traceability addresses a central compliance concern with AI agents: variability without provenance. Deterministic guardrails and explicit reviewer signoff records establish a chain of accountability that can be replayed and validated, particularly for exceptions and overrides. This framing also aligns with NIST-oriented control thinking that emphasizes explainability and access accountability.
Run escrow, insurance, and payment history transfers with managed exceptions
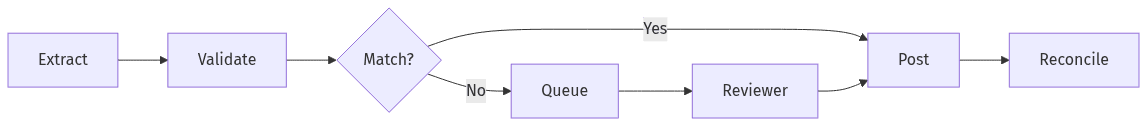 Transfer flow with validation and exception queue
Transfer flow with validation and exception queue
Escrow, insurance, and payment history migration tend to be the highest-friction components of servicing transfer automation because they combine document dependency, mismatch risk, and customer-impact consequences. AI agents can reduce manual classification and reconciliation effort, while RPA can reduce repetitive entry and retrieval, but exception volume remains the primary driver of cycle-time performance. Mature programs treat exceptions as a governed workstream with defined review economics, rather than an edge condition that absorbs the projected ROI.
Core transfer workflow and reconciliation checkpoints
Reconciliation checkpoints typically focus on variances between prior-servicer data, source documents, and the target servicing platform state. Escrow balances, disbursement schedules, insurance coverage dates, and payment histories produce frequent mismatches, while force-placed insurance triggers raise both operational urgency and compliance sensitivity when documentation is incomplete or conflicting.
Exception queues and phased rollout
Exception queues become the control surface for human-in-the-loop governance, since missing documents and data mismatches persist at scale. Phased rollout patterns often appear in vendor-evaluation contexts because confidence depends on predictable triage, SLA-oriented review throughput, and evidence completeness under SOC 2-aligned oversight, rather than on headline automation percentages.
