AWS Well-Architected Remediation for Fintech: A 10-Bucket Backlog to Improve Resilience, Security, and Cost (With Effort & ROI Ranges)
2026-05-13
Build a fintech-focused remediation backlog from your findings
 From findings to a 10-bucket backlog
From findings to a 10-bucket backlog
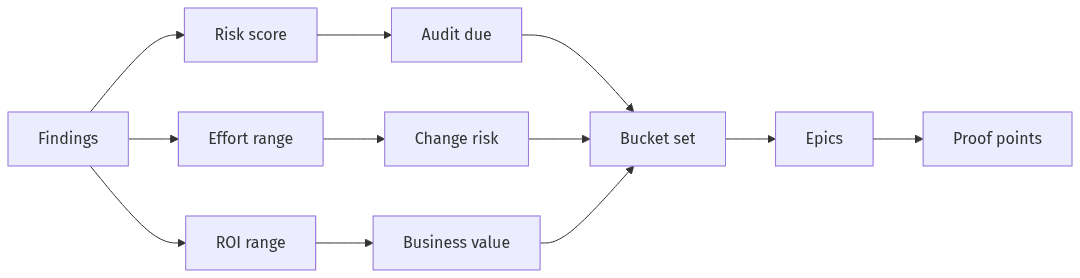
Across regulated fintech environments, an AWS Well-Architected review often yields a volume of findings that exceeds available engineering capacity. The inflection point is when those findings are converted into a risk-based backlog that reflects audit scrutiny, availability expectations, and delivery constraints. Remediation plans that hold up in governance forums read less like a pillar summary and more like a portfolio of verifiable outcomes: reduced blast radius, demonstrable control enforcement, and fewer high-severity operational incidents. Executive visibility improves when each theme carries an effort range and an ROI range that reflects risk reduction alongside cost trade-offs.
How to prioritize for risk, effort, and audit deadlines
Prioritization in fintech typically converges on three pressures: audit expectations, RTO/RPO commitments, and the production-change risk associated with remediation. IAM weaknesses and segmentation gaps often rise to the top because they map directly to common audit exceptions and materially reduce blast radius. Effort and ROI ranges tend to be most defensible when they account for disruption probability and operational impact, rather than treating all remediation as undifferentiated technical debt.
A simple 10-bucket backlog format teams can execute
A 10-bucket backlog format often translates Well-Architected findings into work that aligns engineering, security, and compliance stakeholders. Each bucket typically includes an owner, a target outcome, and proof points that satisfy internal governance and external review. The structure resembles Jira epics in practice: explicit scope boundaries, measurable completion criteria, and artifacts that remain usable through staffing changes and audit cycles.
Buckets 1–3: access and environment separation
 Access control and environment separation overview
Access control and environment separation overview
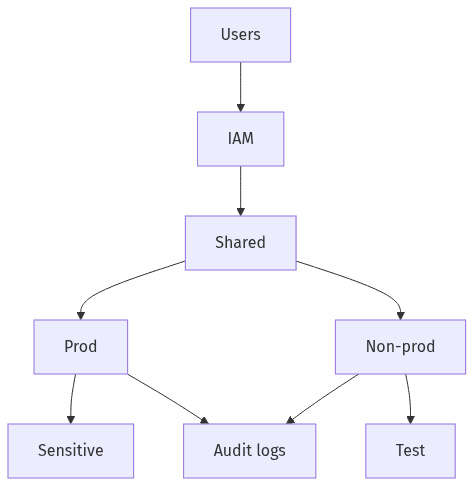
In many AWS-based fintech estates, the quickest audit-driven risk reduction comes from access controls and clearer separation between environments and data domains. Findings in these buckets usually map to “who can do what, where, and when,” plus whether an incident in one area can propagate into regulated workloads. Effort often falls in the low-to-medium range when remediation centers on standardization and consistent enforcement, while ROI frequently trends high because it reduces audit exceptions, narrows exposure, and removes ambiguity during incidents and personnel transitions.
Access basics that auditors look for first
Audit and regulator discussions often concentrate on least privilege, administrative boundaries, and evidence of periodic access review. Recurring flags include overly broad roles, shared or non-attributable access patterns, and unclear handling of emergency or break-glass access. Audit logging becomes a core control because it ties identity decisions to accountability and supports incident retrospectives and third-party examinations.
Separate critical workloads to reduce risk spread
Environment and workload separation often carries more weight in fintech because PCI-aligned scoping and sensitive data handling turn lateral movement into a governance issue, not only a security event. Multi-account boundaries and segmentation controls typically serve as the primary blast-radius mechanisms. The operational effect is usually fewer “all-or-nothing” remediation decisions and clearer ownership by domain.
Buckets 4–6: protect data and reduce change risk
Data protection and change risk sit where security posture meets delivery velocity, which is why these buckets can determine whether remediation work competes with product delivery or reduces rework. Encryption, secrets handling, and release controls recur in Well-Architected findings because inconsistent application is difficult to defend in audits and difficult to manage during incidents. Effort commonly trends medium to high when controls must be applied consistently across accounts and services, while ROI ranges from medium to high due to reduced breach impact and fewer production regressions tied to configuration drift.
Ensure data protection is consistent and provable
Encryption expectations in financial services rarely hinge on intent; they hinge on enforcement and evidence. Gaps often emerge when “mostly encrypted” creates the same operational uncertainty as “not guaranteed,” particularly as service footprints expand. Policy-based enforcement mechanisms (including service control policies where applicable) often separate best-effort controls from controls that can be demonstrated repeatedly during audits.
Manage secrets and releases more safely
Fintech incident reviews often trace production exposure to secrets sprawl and high-privilege change paths rather than a single exploit chain. Release safety becomes a governance concern when emergency fixes bypass standard controls or when sensitive values sit outside a managed lifecycle. Change management maturity frequently appears in audit narratives as evidence that remediation reduces recurring risk instead of producing isolated, one-time fixes.
Buckets 7–10: reliability, response readiness, and cost discipline
Reliability, incident response readiness, and cost governance converge in fintech because downtime carries regulatory, reputational, and direct financial consequences. Even organizations with strong Well-Architected scores can remain exposed when recovery assumptions are untested, observability is fragmented, or spend grows faster than accountable ownership. Effort often falls in the medium-to-high range, particularly where cross-account consistency is required, while ROI tends to remain high due to faster detection, faster recovery, clearer audit narratives, and less waste from unmanaged variability in demand and resource usage.
Validate recovery readiness and operating response
Disaster recovery readiness often serves as the executive “truth test” for RTO/RPO commitments. Regulated workloads typically require more than documented designs; they require artifacts that show readiness and decision-making under stress. Regulator-facing artifacts commonly include stated RTO/RPO targets, evidence of recovery validation, and incident response materials that demonstrate operational control rather than stated intent.
Set clear visibility and cost guardrails
Observability gaps often present as delayed detection, noisy alerting, and limited confidence during post-incident review, while cost issues present as surprise spend and unclear ownership. Centralized visibility and guardrails typically prevent waste from becoming embedded in baseline operations. FinOps alignment often functions as a governance layer that connects engineering autonomy to accountable unit economics.
Scope a short remediation sprint and expected outputs
 Sprint outputs that support audit evidence
Sprint outputs that support audit evidence
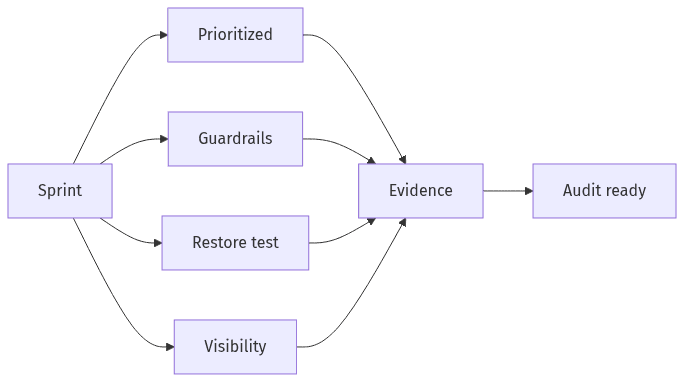
A short, partner-led remediation sprint is often considered when the backlog is understood but internal bandwidth conflicts with audit timelines. A 2–4 week scope typically emphasizes high-leverage control enforcement, reduced production-change risk, and an evidence trail that remains usable in future audits. The commercial rationale is usually the conversion of ambiguous findings into verifiable closure supported by documented proof. For executives, the most relevant outputs tend to be a prioritized backlog with effort/ROI ranges, visible risk-reduction milestones, and standardized artifacts that reduce recurring compliance friction.
A 2–4 week plan to sequence and deliver outcomes
Short engagements typically focus on sequencing that limits production risk and avoids broad refactors that conflict with release cadence. Delivery expectations usually center on closing high-severity findings and establishing guardrails that scale across accounts and environments. The differentiator is verifiability: outcomes that can be validated operationally and communicated in governance forums without reliance on informal tribal knowledge.
What to include in an auditor-ready evidence pack
An auditor-ready evidence pack typically bridges technical remediation and compliance verification. Standardized templates and repeatable artifacts often matter more than volume, particularly under SOC 2 and PCI DSS scrutiny. Typical evidence themes include access governance records, segmentation and boundary rationale, encryption enforcement proof, DR RTO/RPO documentation with validation artifacts, and observability and incident readiness materials that demonstrate ongoing control rather than point-in-time cleanup.
