Microservices vs Modular Monolith for Marketplace Platforms: A Migration Plan That Won’t Break Checkout, Search, or Vendor Payouts
2026-04-20
Choose the right architecture for your marketplace
Marketplace platforms rarely change architecture for its own sake; the decision usually reflects risk tolerance, release pressure, and operating maturity. A modular monolith often preserves predictability for tightly coupled journeys such as checkout, order validation, and payment authorization, while microservices tend to show value when scaling needs and change volume concentrate in specific domains. Executive decision context typically centers on downtime tolerance, auditability expectations, and whether the organization can absorb added operating overhead without shifting risk into higher incident rates or payout failures.
When to keep a modular monolith
A modular monolith commonly fits when marketplace workflows remain tightly intertwined across cart, pricing, promotions, orders, and payments, and when operational simplicity carries material value. Release constraints in these environments often come more from internal coupling, test surface area, and release coordination than from the deployment unit itself. Modularity discipline and delivery fundamentals tend to drive outcomes more than the monolith label.
When microservices start to make sense
Microservices typically start to fit when scaling needs and change cadence diverge across domains, especially where search demand, integration churn, or payout-logic volatility create recurring bottlenecks. The upside generally comes from domain isolation and fault containment, not automatic throughput in delivery. Checkout stability, search SLAs, and payout correctness often become the constraints that determine where separation yields net value.
Clarify marketplace domains and ownership
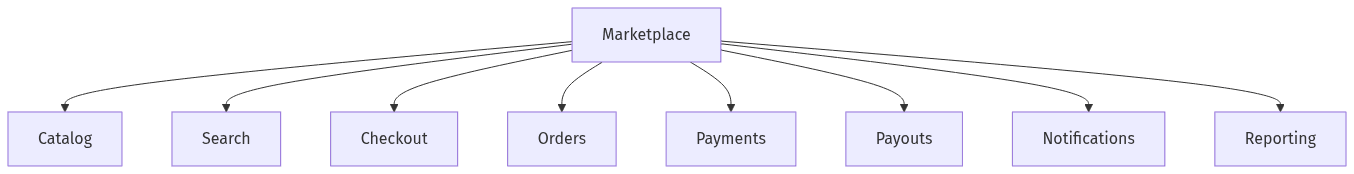 Marketplace domains and clear ownership areas
Marketplace domains and clear ownership areas
Architecture outcomes in marketplaces often track back to domain boundaries more than deployment topology. Catalog, search, cart/checkout, orders, payments, and vendor payouts carry distinct correctness thresholds, latency expectations, and compliance implications. Clear ownership tends to reduce ambiguous dependencies that otherwise surface as regressions, slowdowns in release cadence, and post-deployment payout issues. In executive terms, domain clarity functions as governance: it narrows blast radius, makes accountability explicit, and makes reliability measurable where commercial risk is incurred.
Define clear product areas and responsibilities
Bounded contexts from domain-driven design often map cleanly to marketplaces because the business already segments around catalog merchandising, buyer experience, order lifecycle, and settlement. Orders, payments, and payouts form a particularly sensitive chain due to correctness and audit requirements. Shared business rules across these areas frequently correlate with rollout risk, because small changes can leak into checkout behavior or payout outcomes.
Reduce shared-data reliance over time
Shared databases often create the most persistent coupling in marketplace platforms, even when services or modules look separated at the code level. Early modernization phases commonly preserve some shared-data constraints, but long-term autonomy typically depends on clear data ownership. The recurring issue is cross-domain queries and implicit joins, which can erode isolation, complicate incident triage, and reintroduce release coordination.
Sequence changes to reduce risk and avoid rewrites
 Low-risk first sequencing for marketplace migrations
Low-risk first sequencing for marketplace migrations
Incremental modernization patterns such as Strangler Fig generally align with marketplace realities because revenue-critical paths resist disruption. Sequencing often reflects a pragmatic tradeoff: early separation tends to favor domains with frequent change and limited impact on checkout correctness, while deferring areas where distributed consistency becomes costly. Sequencing also influences organizational confidence, because early progress needs to appear without creating new outage modes or expanding compliance exposure across payment and settlement flows.
Good early targets to separate
Search, payouts, notifications, third-party integrations, and reporting frequently surface as early candidates because change rates can be high while coupling to core order placement can remain contained. Search often carries performance and SLA pressure, and payout isolation often reflects correctness and auditability requirements. These domains can support clear boundaries and testable outcomes without forcing an immediate redesign of the full checkout path.
Areas to delay until the team is ready
Checkout and core order processing commonly remain late candidates because they concentrate transactionality, compliance implications, and buyer-facing failure risk. In these areas, distributed transactions and consistency tradeoffs become unavoidable, and operational gaps show up quickly as revenue-impacting incidents. Readiness tends to correlate with observability depth, incident response clarity, and confidence in rollback behavior under production traffic.
Migrate safely with incremental rollout and checkpoints
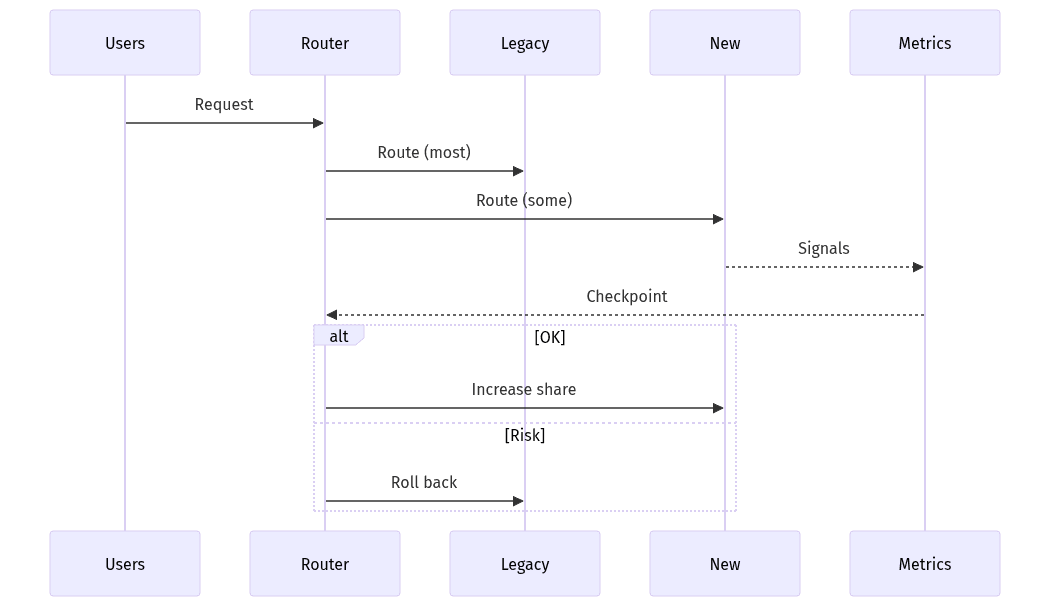 Incremental rollout with checkpoints and rollback
Incremental rollout with checkpoints and rollback
Marketplace modernization risk often shifts from code changes to rollout behavior once domains begin separating. Progressive delivery and incremental cutovers generally act as risk controls because customer experience and revenue exposure stay bounded. The executive lens often focuses on two questions: whether rollback remains credible under partial cutover, and whether visibility exists to distinguish a localized service issue from systemic checkout degradation. In regulated areas, auditability expectations and PCI scope constraints add friction to change cadence.
Introduce changes in controlled steps
Incremental rollouts typically depend on backward compatibility, stable interfaces, and explicit cutover gates tied to measurable signals rather than calendar targets. Strangler-style transitions can cap rewrite risk by keeping existing behavior in place while new capabilities assume responsibility gradually. A recurring failure mode is asymmetric impact: small rollout errors can disproportionately affect checkout completion or vendor payout success.
Ensure operational readiness for the new setup
Microservices increase the surface area for reliability management, making observability and incident response central to business risk rather than an engineering afterthought. Logging, metrics, and tracing often determine whether issues are contained quickly or linger as revenue-impacting ambiguity. On-call readiness and explicit operational ownership tend to matter most in payouts and payments-adjacent domains, where correctness and audit trails can intersect with SOX-style expectations.
Measure outcomes and decide whether to continue
Architecture migration in marketplaces tends to hold when continuation depends on measurable outcomes rather than momentum. Release velocity and scalability matter, but reliability signals often dominate because checkout disruption and settlement errors carry immediate financial and reputational cost. Measurement also corrects the assumption that microservices inherently increase delivery speed; speed typically appears only when coupling declines without a matching increase in operational drag. A KPI-driven approach often turns “modernization” into a portfolio decision evaluated per domain.
Track the marketplace scorecard that matters
Scorecards typically combine release frequency, change failure rate, incident volume, and p95/p99 latency for search and checkout-adjacent endpoints. Vendor payout success rates and reconciliation exceptions often provide the clearest signal of isolation quality and auditability. Business linkage usually centers on search performance versus conversion and on checkout stability versus GMV protection, even when the technical work occurs outside those paths.
Set clear go/no-go criteria per phase
Go/no-go decisions commonly reflect whether complexity remains proportional to demonstrated value: fewer regressions, faster safe releases, improved latency, and fewer payout failures. Pauses frequently follow signals such as longer incident duration, unclear ownership during outages, or persistent coupling through shared data. In marketplace environments, continuation typically requires evidence that risk to checkout and settlement declines as migration proceeds.
