Productionizing a Multi-Tenant React App on AWS: A DevOps Playbook for B2B SaaS (SSO, Tenant Isolation, Monitoring, and Release Safety)
2026-05-12
Define tenant separation and protect performance
 Hybrid tenant separation with shared and dedicated paths
Hybrid tenant separation with shared and dedicated paths
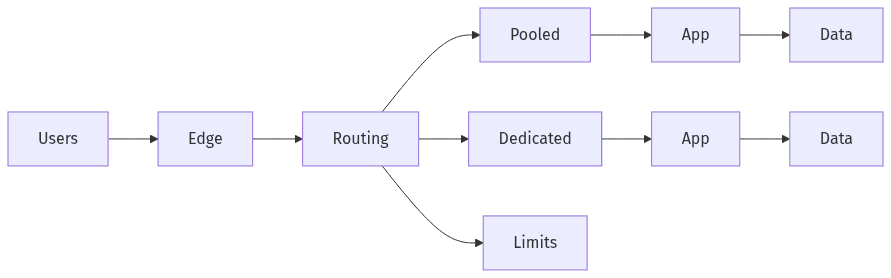
Operating a multi-tenant React application on AWS tends to hinge on how explicitly tenant boundaries are defined and how predictable shared-resource behavior remains under load. Tenant isolation spans data planes, compute, network paths, and IAM, and the operational objective is a measurable reduction in blast radius rather than conceptual separation. Executive teams often navigate a cost profile versus the assurance levels enterprise buyers expect during security review. Performance protection is tightly coupled to isolation, because scale pressure commonly shows up first as cross-tenant contention rather than a clear capacity shortfall.
Choose a model that fits your customers
Multi-tenancy choices typically land in pooled, siloed, or hybrid models, with enterprise tiers driving the strictest separation expectations. Hybrid patterns often emerge when low-friction onboarding matters for SMB segments while premium customers require tighter boundaries. The decision logic usually centers on auditability, tenant-specific risk tolerance, and operational overhead, not on any single AWS service selection.
Avoid noisy-neighbor issues early
Noisy-neighbor risk usually appears when a small subset of tenants consumes disproportionate shared limits, driving latency spikes and cascading timeouts that look “random” at the product layer. Quotas, per-tenant rate limiting, and resource partitioning operate as reliability controls as much as cost controls. Without explicit limits, incident duration often increases because root cause attribution becomes ambiguous across shared infrastructure.
Make enterprise login reliable across tenants
 SSO flow with tenant mapping and authorization
SSO flow with tenant mapping and authorization
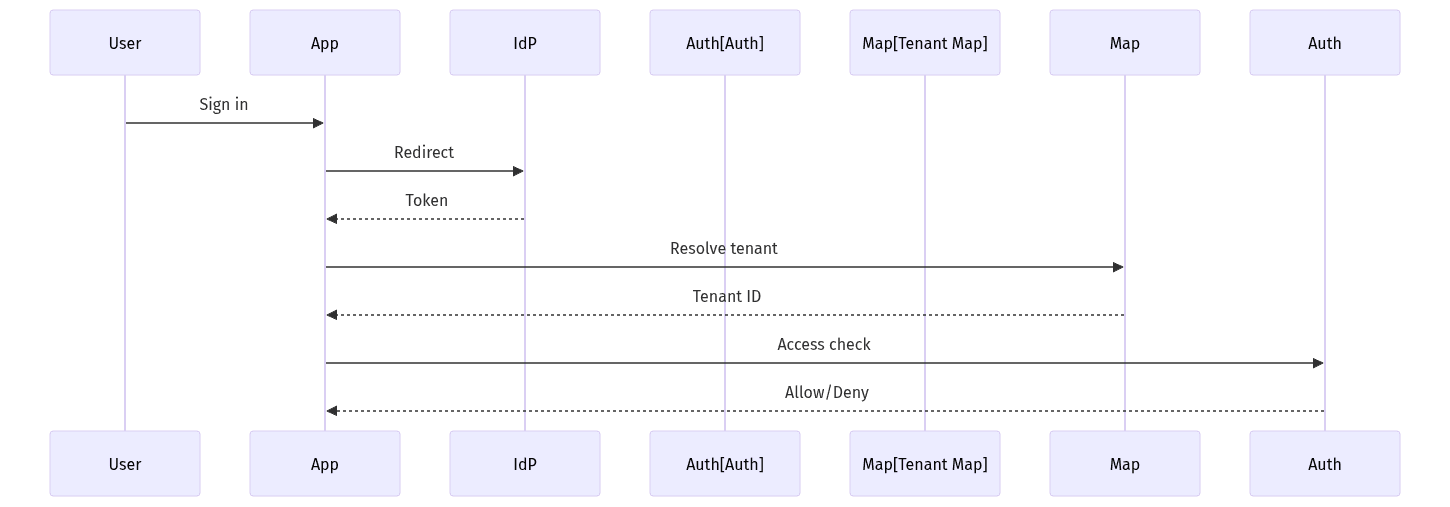
Enterprise SSO becomes an operational concern once multiple tenants introduce multiple identity providers, differing security postures, and shifting claim conventions. In AWS-hosted SaaS, SAML 2.0 and OIDC often coexist, with Cognito or custom authentication stacks serving as the integration surface while tenant mapping remains application-owned. Reliability matters because SSO incidents are indistinguishable from outages to enterprise buyers and frequently trigger escalations during procurement. Over time, identity drift becomes routine, turning “set-and-forget” assumptions into ongoing support load and security exposure.
Plan your SSO approach
SSO designs often depend on stable tenant-to-identity binding across providers, including multi-IdP tenants created by acquisitions, geographic divisions, or parallel business units. Token and session semantics affect both security posture and support load, particularly when tenant context is derived from claims that vary across IdPs. Provisioning expectations, including SCIM, often shape enterprise readiness more than the user interface.
Handle common SSO risks
Recurring SSO failure modes include IdP metadata drift, inconsistent attribute and claim mapping, and ambiguous logout behavior, each of which can lead to intermittent access denial or unintended access persistence. Least-privilege IAM and audit logging become part of the identity posture because enterprise security reviews look for control evidence rather than feature parity. Overreliance on “Cognito completeness” also tends to mask application-level authorization gaps.
Improve support with tenant-aware visibility
 Tenant context across logs, metrics, and traces
Tenant context across logs, metrics, and traces
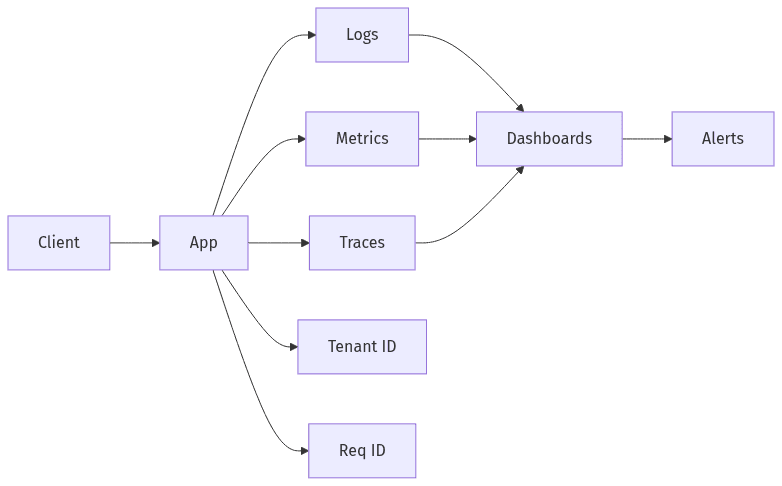
Observability in a multi-tenant AWS stack becomes more useful when it answers tenant-scoped questions quickly: which tenant is affected, what changed, and where latency or errors originate. Without tenant-level visibility, incident response commonly defaults to global mitigations that widen customer impact. Metrics, logs, and traces become more usable when they carry consistent tenant context and correlation identifiers across boundaries. Cost dynamics matter as well; high-cardinality dimensions and unsampled traces can raise observability spend faster than infrastructure spend during growth phases.
Keep tenant context consistent
Tenant context propagation functions as a safety property as much as a debugging aid, because inconsistent attribution increases the risk of cross-tenant data exposure and misrouted authorization decisions. A single tenant identifier and correlation ID across services supports trustworthy end-to-end traces, whether via X-Ray or OpenTelemetry. Middleware defects frequently sit behind “impossible” support tickets.
Use views and alerts that support SLAs
Tenant-aware dashboards and alerts often reduce time to resolution by narrowing scope immediately, especially when service commitments vary by customer tier. Tagging conventions across CloudWatch logs, metrics, and traces provide the basis for per-tenant SLO tracking and alert routing. Without those conventions, on-call noise rises and enterprise SLA discussions become harder to substantiate.
Protect app settings and access
Secrets and configuration sprawl often grows with tenant count, new integrations, and environment proliferation, converting operational convenience into security and reliability exposure. AWS-native services such as KMS, Secrets Manager, and Parameter Store commonly serve as the control plane for sensitive values, while tenant-specific configuration introduces a second axis of complexity. Enterprise buyers expect evidence of encryption, access traceability, and least-privilege controls, not only the presence of managed services. Mis-scoped permissions and shared secrets remain frequent root causes of multi-tenant incidents.
Organize secrets and configuration
Clear separation between platform-wide secrets and tenant-specific values reduces the likelihood of accidental cross-tenant exposure and supports a clean audit narrative. Tenant configuration often includes identity settings, integration credentials, and feature entitlements, each with different rotation and access patterns. Treating all configuration as equivalent increases operational error rates and compliance friction.
Control access and keep it current
Least-privilege IAM, scoped KMS policies, and audited access paths create a defensible posture when enterprise security teams assess multi-tenant risk. Ongoing change is a persistent risk factor because permissions and secrets often evolve faster than documentation in many organizations. CI/CD and IaC influence this area primarily through consistency and traceability, reducing untracked changes that surface during incidents.
Ship changes safely and be ready to review
Release safety is a defining competency for B2B SaaS on AWS because deployment-related outages tend to erode renewal confidence more than isolated functional defects. Blue/green and canary patterns commonly appear in mature environments, with feature flags adding separation between code rollout and customer-facing exposure. Data migration risk remains a primary constraint on “zero downtime” narratives, since backward compatibility often determines whether rollback is feasible. A readiness lens also matters commercially, because enterprise onboarding frequently coincides with closer scrutiny of operational controls, logging, and recovery posture.
Release with low disruption
Lower-disruption releases tend to correlate with smaller blast radius, faster rollback, and clearer separation between deployment events and feature activation. Canary and blue/green approaches usually reduce the chance that a single change affects every tenant at once. Rollback quality often becomes the differentiator, since migration coupling and tenant-dependent behavior can otherwise narrow recovery options.
Use a readiness checklist before scaling
A structured readiness review often serves as a translation layer between engineering constraints and enterprise procurement expectations, particularly around SOC 2-style control evidence and least-privilege access. Tenant isolation guarantees, SSO reliability, per-tenant observability, and release safety commonly surface as headline themes in those conversations. An AWS multi-tenant architecture review and DevOps build-out plan often becomes the practical next step when gaps surface during that assessment.
