PCI-Aware AI Automation for Payment Disputes & Refund Workflows: Reference Architecture + Vendor Evaluation for US Fintech
2026-05-12
Set goals and boundaries before automating disputes and refunds
Dispute and refund automation holds up best when business outcomes and risk limits are explicit upfront, since early design choices often determine PCI DSS scope and ongoing audit burden. In many US fintech environments, pressure to compress time-to-resolution and lower cost per case often collides with strict expectations for cardholder data handling, logging, and retention. A clear boundary between what belongs inside the cardholder data environment (CDE) and what remains outside it tends to shape downstream decisions, from evidence ingestion to LLM-enabled triage. When boundaries are left implicit, automation efforts often expand PCI scope unintentionally and create uneven controls across teams and vendors.
Workflow scope and performance baseline
Chargebacks, refunds, and representment often span multiple case types, queues, and handoffs, with SLAs shaped by external network deadlines and internal approval paths. A usable performance baseline typically covers current cycle time, rework rates, exception volumes, and cost per case so automation impact can be tied to operating expense and staffing load. Misalignment between workflow scope and service expectations is a recurring failure mode: automation optimizes one segment while downstream teams inherit new queues, escalations, or reconciliation work.
Sensitive data boundaries
Sensitive data boundaries often matter more than model selection because they determine whether automation reduces exposure or multiplies it. In PCI-scoped environments, minimization commonly treats raw PAN and other cardholder data as “never leave the CDE,” relying on tokenization or redaction for downstream handling and analytics. Ambiguity about where data resides, how long it persists, and what enters prompts, logs, or telemetry frequently becomes the root cause of audit friction and preventable leakage risk.
High-level architecture for safe triage and system updates
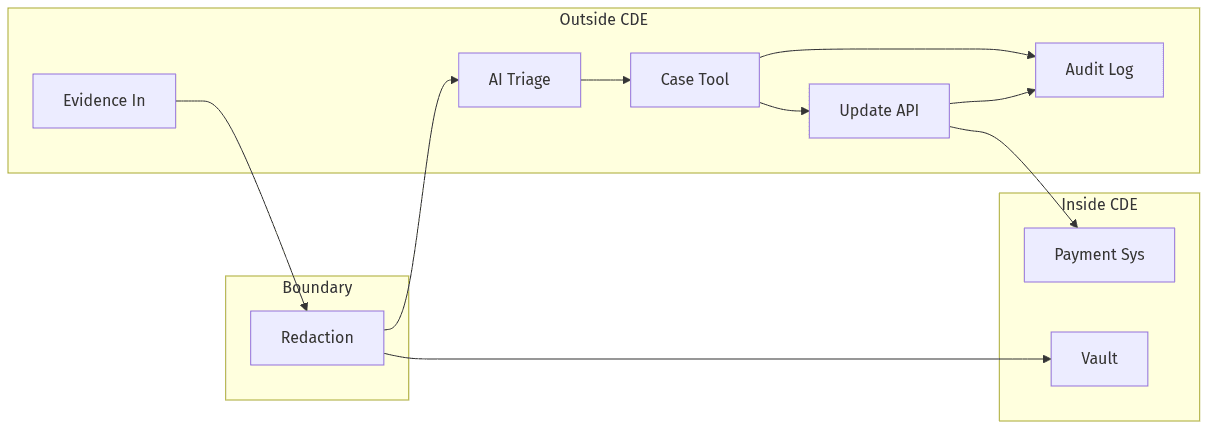 Separate sensitive systems from AI triage and case updates
Separate sensitive systems from AI triage and case updates
PCI-aware reference architectures typically separate dispute intelligence from payment-sensitive systems to preserve operational speed without pulling AI components into the CDE. The separation often resembles a three-zone model with explicit trust boundaries, where data minimization occurs before any LLM-based classification, summarization, or decision support. Reliability requirements also drive architecture choices because dispute operations depend on consistent state across case management, payment processors, core banking, and CRM. When boundaries and synchronization semantics are underspecified, teams often see duplicated cases, mismatched outcomes, and audit trails that do not reconcile across systems.
Input capture and safe handling
Evidence capture commonly involves emails, PDFs, and attachments that mix operational context with regulated data, creating a high-risk ingestion surface. Safer handling patterns generally rely on redaction or tokenization before any LLM exposure, with an explicit expectation that raw PAN does not enter prompts, logs, or model telemetry. Control gaps often surface when document parsing, OCR output, or unstructured text fields bypass redaction assumptions and are forwarded downstream unchanged.
System updates and operational reliability
Dispute outcomes typically require authoritative updates across multiple systems of record, including processor portals, core ledgers, and customer communication systems. Operational reliability usually depends on consistent identifiers, idempotent updates, and controlled retries to prevent drift between case status, financial posting, and customer-facing records. Integration failure modes often appear as conflicting states that distort SLA reporting and weaken confidence during audit reviews.
Security and audit readiness essentials
In dispute and refund automation, security posture is typically judged less by broad “AI safety” positioning and more by demonstrable controls aligned with PCI DSS 4.0 expectations and common fintech audit practices. Durable programs usually emphasize scope reduction, encryption and key management discipline, controlled retention, and logging that can be traced end-to-end during review. Audit readiness often depends on consistent evidence, particularly when multiple vendors participate in data handling or workflow execution. Weaknesses regularly emerge in overlooked surfaces such as model telemetry, debug logs, and long-lived storage of extracted evidence, each of which can quietly expand exposure.
Protect data and reduce exposure
Exposure reduction generally comes from minimizing stored sensitive content, constraining sharing paths, and keeping processing outside the CDE where feasible. In LLM-enabled systems, telemetry scrubbing becomes a focal control because prompts, outputs, and intermediate artifacts can carry regulated fields into logs and monitoring tools. Encryption in transit and at rest, paired with disciplined secrets and key management, tends to distinguish audit-ready implementations from programs that rely primarily on written policy.
Access controls and audit evidence
Least-privilege access and separation of duties are most critical around refund approvals and dispute reversals, where financial impact and fraud risk converge. Audit evidence usually centers on who performed which action, under what authority, and with which supporting artifacts, with tamper-evident logs serving as the system record. Inconsistent RBAC, shared accounts, or missing approval history commonly weakens both PCI narratives and internal control reviews.
Guardrails and human approvals to reduce errors
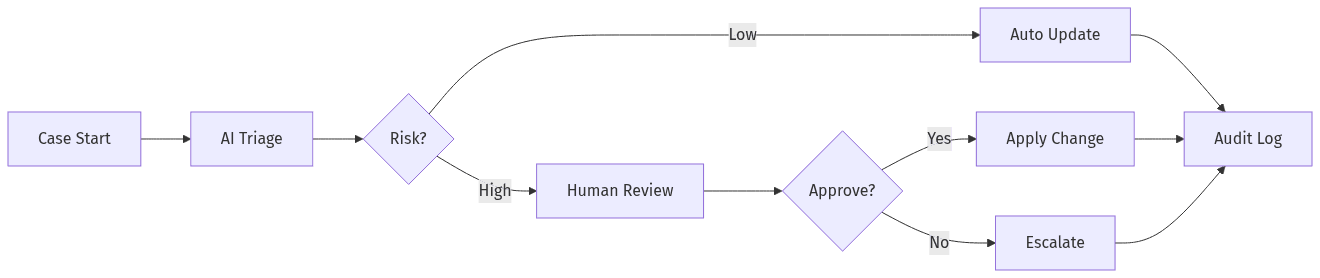 Maker-checker approvals for higher-risk dispute outcomes
Maker-checker approvals for higher-risk dispute outcomes
LLM-enabled dispute triage can speed classification and summarization, but risk concentration rises as model outputs move closer to financial decisions. Guardrails often operate as policy boundaries that limit autonomous outcomes, with human-in-the-loop approvals creating accountable decision points for exceptions, reversals, or high-dollar refunds. Executive scrutiny typically shifts from “Can automation work?” to “Can automation fail safely?” because hallucinations, misclassification, and edge-case evidence can trigger incorrect routing, missed deadlines, or unauthorized credits. Accountability mechanisms tend to determine whether automation tightens controls or simply relocates them.
Safe decision limits and approvals
Higher-risk outcomes in disputes and refunds typically sit behind maker-checker patterns and dual control, particularly when exceptions deviate from policy or when evidence is ambiguous. Decision limits often separate low-risk informational assistance from actions that change balances, alter dispute posture, or trigger customer refunds. Control credibility generally depends on consistent logging of approvals, overrides, and escalation paths rather than informal checkpoints.
Quality and SLA oversight
SLA oversight relies on operational visibility into case aging, queue health, and exception rates because dispute operations are deadline-driven and cross-functional. Quality signals often include decision accuracy, rework frequency, and representment success indicators tied to evidence completeness and timeliness. Without sustained review and transparent reporting, automation can mask failure patterns until SLA breaches or audit sampling surfaces gaps.
Choosing vendors for PCI-aware automation
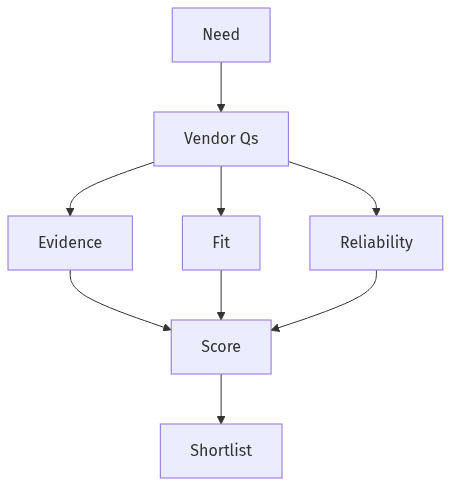 Vendor scorecard balances evidence, fit, and reliability
Vendor scorecard balances evidence, fit, and reliability
Vendor selection for PCI-aware automation typically turns on verifiable evidence rather than assurances because compliance responsibility remains with the fintech even when functions are outsourced. Procurement and security teams often require review-ready artifacts showing how sensitive data is handled, where it persists, and how access and logging controls operate under real operating conditions. Fit matters as well: dispute workflows touch core banking, payment processors, and CRM, and limited integration support can create operational drift that offsets automation benefits. A credible shortlist usually balances security posture, auditability, and reliability under SLA pressure rather than treating model performance as the primary criterion.
Security and audit evidence
Audit-ready vendors typically provide concrete artifacts around PCI DSS alignment, SOC 2 controls, and operational practices such as logging, retention, and access control. Evidence often includes documented data boundaries, explicit statements on model telemetry handling, and the ability to walk through controls during security reviews. Gaps frequently appear when vendors claim “PCI compliance” at a high level without clear scope statements or verifiable attestations such as an AOC where applicable.
Fit, rollout plan, and support
Integration readiness often differentiates vendors in dispute and refund automation because accurate synchronization back to processors, core systems, and CRM determines operational truth. Executive confidence usually depends on clear ownership models, support responsiveness, and a path from early pilot behavior to production reliability under audit and control expectations. A common disappointment pattern is a strong demo that lacks the operational depth required for exception handling, escalation, and maintenance in a regulated fintech environment.
