SAML SSO + SCIM Provisioning for B2B SaaS: React + AWS Reference Architecture for Enterprise Deals (Okta/Azure AD)
2026-05-16
Define what “enterprise-ready” identity means for your SaaS
Enterprise procurement typically treats identity as an entry requirement, not a product differentiator, and “enterprise-ready” usually means more than a working SAML login. Okta and Azure AD evaluations commonly expect SAML SSO alongside SCIM 2.0 lifecycle management, tenant-safe authorization, and evidence that security teams can review. In multi-tenant SaaS, identity maturity is often assessed as a risk-control surface: buyer confidence depends on predictable onboarding, explicit tenant boundaries, and controllable offboarding. Product and deal timelines tend to intersect here, because identity gaps reappear as security-review delays, escalation cycles, and per-tenant exceptions.
Choose SSO, provisioning, and first-login setup
Enterprise identity scope usually separates authentication from lifecycle control. SAML SSO covers login expectations, while SCIM provisioning supports join-change-leave requirements that IT administrators treat as baseline. Just-In-Time provisioning can reduce friction at first login, but it rarely covers deprovisioning, access-drift control, or license recovery expectations without SCIM-based lifecycle signals.
Confirm tenant separation and account safety expectations
Multi-tenant isolation makes SSO an authorization concern as much as an authentication concern. Tenant-binding assumptions, attribute trust boundaries, and server-side enforcement determine whether SSO becomes a cross-tenant exposure path. Security reviewers routinely look for explicit descriptions of how assertions translate into tenant and role membership, and how common account-takeover paths are constrained.
High-level architecture for SSO and provisioning
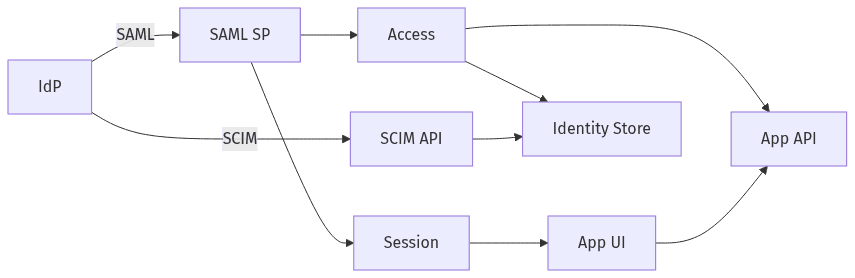 Where SAML login and SCIM admin updates connect
Where SAML login and SCIM admin updates connect
A React + AWS SaaS reference architecture typically treats the identity layer as a contract between external IdPs and tenant-aware backend authorization. React carries user experience and session continuity, while tenant authority generally sits in backend services that validate SAML assertions, issue application sessions, and centralize access decisions. SCIM endpoints sit alongside application APIs as an administrative control plane, reflecting directory state into the SaaS identity store. This separation limits client-side trust and contains the impact of claim variability across Okta and Azure AD configurations.
Key parts and responsibilities
Enterprise-ready designs commonly separate three responsibilities: SAML integration at the Service Provider boundary, a tenant-aware identity store for users and memberships, and an authorization layer enforcing RBAC and entitlements. IdP-specific differences usually concentrate in claim and group normalization rather than spreading through application logic, reducing long-term maintenance and per-tenant customization pressure.
User sessions and app access basics
Session management usually becomes the source of tenant context after a SAML login, rather than relying on tenant signals stored in the browser. Backend-issued sessions and server-side authorization checks reduce dependence on client routing or UI state for access control. Security reviews often center on this boundary, because client-side tenant authority is a recurring precursor to cross-tenant access.
Tenant-aware access mapping for SAML logins
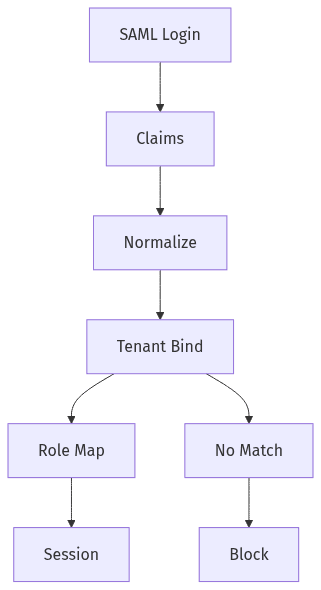 How SAML claims map to tenant and role safely
How SAML claims map to tenant and role safely
SAML assertions typically carry enough information for authentication, but not always enough for durable, tenant-safe authorization. Enterprise SaaS identity commonly depends on an explicit tenant-binding contract that maps IdP claims to organization membership and role assignment without depending on heuristics such as email domain alone. Mapping drift is a recurrent risk when group names, object identifiers, or claim availability vary by tenant configuration. A stable mapping model constrains privilege escalation, reduces support escalation loops, and yields more consistent artifacts for SOC 2-aligned access-control narratives.
User and role mapping approach
A consistent mapping model typically treats tenant membership as an explicit binding rather than an inferred property of a login. Email collisions across tenants, shared domains, and acquisitions can invalidate assumptions that look reasonable in early-stage SaaS. RBAC assignments often depend on normalized group or attribute signals, combined with server-side checks that prevent assertion content from acting as a direct authorization grant.
Support Okta and Azure AD with one approach
Okta and Azure AD often differ in claim formats, group representations, and administrator defaults, even when both present SAML 2.0 support. A unified approach generally normalizes claims and group signals into a consistent internal model, allowing enterprise tenants to vary IdP configuration without forcing IdP-specific application logic. This reduces edge cases that predictably surface during enterprise onboarding.
Provisioning lifecycle with SCIM and clean offboarding
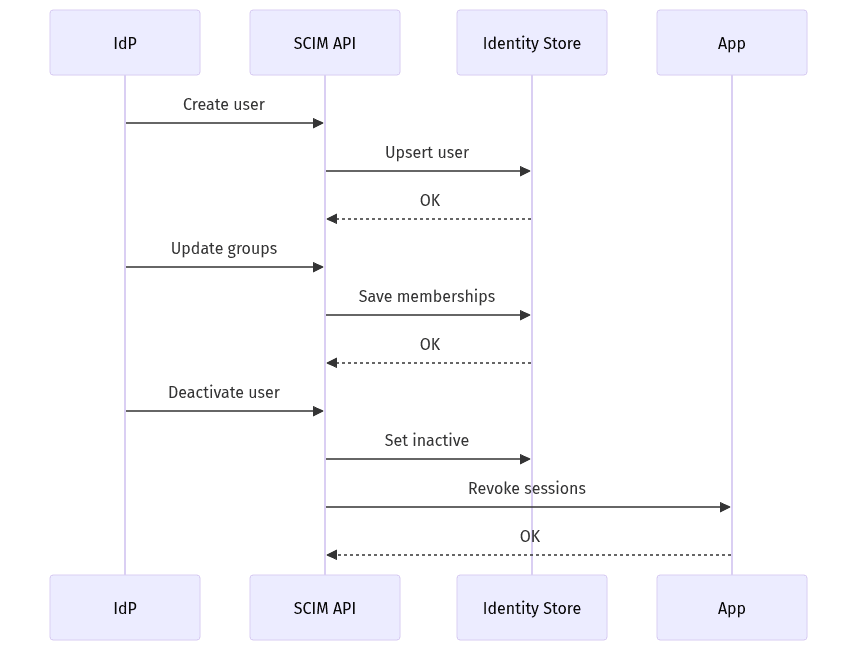 SCIM lifecycle: create, update, deactivate
SCIM lifecycle: create, update, deactivate
SCIM 2.0 often functions as the operational backbone for enterprise identity governance, extending beyond account creation into ongoing alignment between directory state and SaaS access. In multi-tenant SaaS, provisioning aligns user presence and group membership with tenant authorization and creates a predictable administrative surface for audits and escalation handling. Join and change events affect access accuracy, while leave events define security posture and cost containment. Enterprise buyers commonly evaluate SCIM maturity by offboarding speed, correctness under retries, and confidence that access does not persist after deactivation.
User and group provisioning basics
SCIM Users and Groups representations typically become the canonical feed for account state and membership within an enterprise tenant. Partial failures and retries are routine in directory-driven integrations, and drift risk rises when group signals are ambiguous or inconsistent. Stable identifiers and normalization reduce the likelihood that directory changes translate into unintended access changes.
Deactivation and license recovery
Deactivation typically carries two enterprise expectations: timely access removal and predictable license recovery. Security teams focus on lingering sessions, tokens, or cached permissions that outlive directory offboarding, while procurement and administrators focus on license counts remaining accurate. Deprovisioning gaps create compliance exposure and commercial friction when identity state no longer matches contractual entitlements.
Operational readiness for security reviews and rollout
Security reviews and enterprise rollout cycles often turn identity into an evidence exercise as much as an engineering deliverable. Auditability, traceability, and retention expectations commonly shape SSO and SCIM event records, including actor, tenant, and correlation identifiers. Rollout also introduces commercial risk in B2B SaaS, since existing customers expect continuity while enterprise tenants require stricter controls. A phased migration posture can reduce disruption and support load, while preserving fallback login options that prevent lockouts during IdP changes or misconfiguration.
Logging and monitoring expectations
Audit logs often serve as the shared vocabulary between engineering, security, and compliance during SOC 2-style reviews. SAML logins, assertion outcomes, provisioning changes, deactivations, and administrative actions typically need consistent entries tied to tenant and request identifiers. Monitoring expectations commonly include anomaly visibility and the ability to reconstruct identity events without ambiguity.
Phased rollout with safe fallback access
SSO adoption across an installed base often benefits from gradual tenant enablement, because IdP configuration quality varies and misconfiguration can create lockout risk. Fallback authentication frequently remains a safety valve during migration, especially while administrators validate claims, groups, and domain assumptions. Enterprise credibility tends to increase when these controls read as deliberate risk management rather than one-off exceptions.
