MongoDB to Postgres on AWS for B2B SaaS: A Migration Playbook to Fix Reporting, Reduce Spend, and Enable Reliable Billing
2026-05-08
Decide if migration is worth it for reporting, billing, and spend
In many B2B SaaS organizations, the business case for a MongoDB to PostgreSQL migration on AWS concentrates around three pressures: reporting credibility, billing correctness, and managed database spend. Reporting pain often shows up as uneven dashboard latency and KPI definitions that drift between teams as document shapes change over time. Billing risk tends to surface as invoice disputes, revenue leakage, and audit friction when critical fields vary by tenant, plan, or product version. Cost pressure commonly arrives with scale, when operational overhead and growth in read-heavy analytics expand the overall MongoDB footprint.
Signs it’s time to move
Recurring reporting delays, frequent “data doesn’t match” escalations, and repeated billing corrections often indicate a mismatch between schema-less storage and finance-grade data expectations. Incident histories and baseline KPIs commonly show the same pattern: expensive ad-hoc aggregation, inconsistent document shapes, and repeated operational intervention that competes with roadmap delivery and customer commitments.
Define success and decision checkpoints
Executive alignment typically depends on measurable outcomes tied to accuracy, latency, and cost. Finance-approved correctness criteria becomes the anchor, particularly for invoices, credits, and usage calculations. Decision checkpoints usually map to explicit gates for parity thresholds, tolerable replication lag during a parallel run, and a defined point at which rollback remains viable without extending customer impact.
Choose the right AWS PostgreSQL option for your SaaS
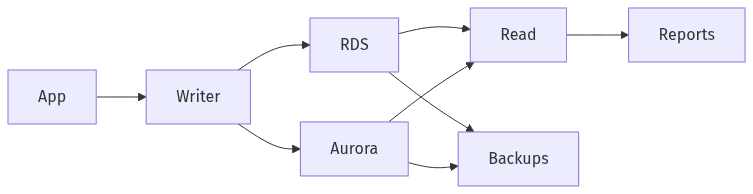 RDS vs Aurora in a simple SaaS context
RDS vs Aurora in a simple SaaS context
AWS options for PostgreSQL typically narrow to RDS for PostgreSQL and Amazon Aurora PostgreSQL, with tradeoffs shaped by write patterns, availability targets, and spend predictability. Evaluation tends to center less on feature matrices and more on operational fit: durability characteristics, scaling behavior under mixed OLTP and reporting workloads, and how cost behaves under steady-state versus bursty demand. Organizational preference also matters, since platform teams often weigh standardization, existing observability conventions, and risk tolerance around managed-service boundaries in production.
RDS vs Aurora at a high level
RDS is commonly treated as the baseline managed PostgreSQL offering, while Aurora often becomes relevant when availability targets and scaling behavior are tighter. Cost tradeoffs usually track with workload volatility and sustained throughput. Write intensity and read amplification from analytics often drive which option produces fewer operational surprises.
Plan for reliability and daily operations
Reliability expectations in B2B SaaS typically extend beyond uptime into auditability and tenant isolation. Backups, access controls, and monitoring conventions become tied to commercial risk, particularly where SOC 2 and GDPR considerations apply. Operational signals such as replication lag, error rates, and mismatch rates often function as executive-facing indicators of stability during migration windows.
Design Postgres data for multi-tenant reporting and billing accuracy
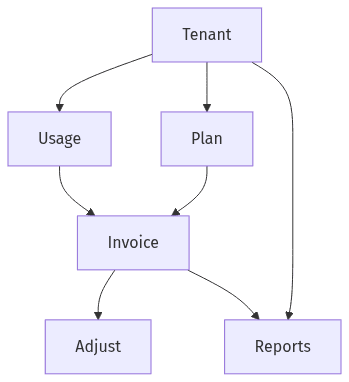 Tenant isolation supports billing and reporting trust
Tenant isolation supports billing and reporting trust
Relational modeling matters most when reporting and billing depend on stable definitions across tenants and over time. PostgreSQL constraints and deliberate indexing reduce ambiguity that accumulates in schema-less collections, particularly when product evolution introduces optional fields and nested structures. In B2B SaaS, the data model often becomes a cross-functional contract between engineering, finance, and RevOps: tenant isolation must remain defensible, reporting must remain reproducible, and billing records must remain traceable through disputes and audits without interpretive gaps.
Multi-tenant data separation
Multi-tenant separation discussions typically converge on preventing cross-tenant leakage while keeping analytics queries predictable. Consistent tenant identifiers and enforced relationships generally increase confidence in dashboards and internal reporting SLAs. Weak isolation guarantees tend to create security and compliance exposure that becomes an executive-level concern.
Billing records you can trust
Billing data often benefits from a ledger-like structure that preserves an auditable chain from usage events to invoice line items and adjustments. Explicit joins and constraints reduce downstream disputes by narrowing interpretation. Reconciliation-friendly representation supports audit expectations and provides a stable basis for revenue recognition inputs without dependence on document variability.
Run MongoDB and Postgres in parallel, then verify results
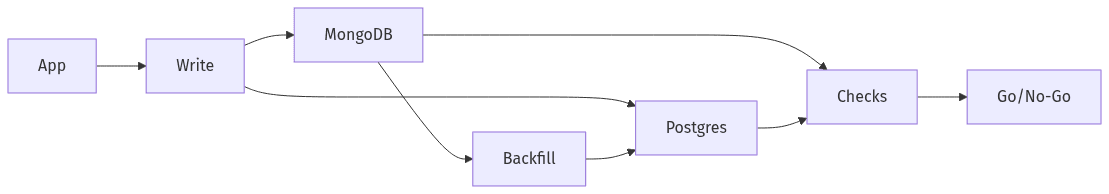 Parallel-run with parity checks before cutover
Parallel-run with parity checks before cutover
A parallel-run period often becomes the risk-management centerpiece of a MongoDB to PostgreSQL migration on AWS, particularly when near-zero downtime is a requirement. Commercial exposure typically concentrates around data divergence: even low mismatch rates can translate into billing errors, support load, and delayed closes. Tooling such as CDC pipelines and AWS DMS frequently appears in plans, but scrutiny usually centers on measurable validation rather than assumptions. Parity metrics, reconciliation reports, and mismatch thresholds become the shared language across engineering and finance.
Keep new data consistent during parallel-run
Consistency for new writes becomes fragile when two systems accept production traffic, since split-brain behavior and retry semantics can compound under load. Idempotency expectations and error-handling policies often determine whether divergence stays limited and diagnosable. Monitoring attention commonly centers on replication lag, error rates, and clearly defined paths for mismatch escalation.
Move historical data and confirm parity
Historical backfill carries performance and correctness risk because production MongoDB workloads can be sensitive to read pressure and document variability. Validation usually prioritizes billing-critical datasets ahead of broader analytics, reflecting the higher cost of finance-facing errors. Checksums, reconciliation summaries, and exception counts often provide the executive-level visibility required for confidence.
Cut over safely with rollback readiness
Cutover risk usually concentrates in a short window where customer impact, revenue exposure, and cross-team coordination converge. Executive confidence depends on clear ownership, rapid verification signals, and a rollback position that remains credible under time pressure. A recurring failure mode is not the lack of a rollback concept, but a lack of specific stop-the-line criteria, including which mismatch rates, latency regressions, or billing anomalies invalidate the cutover. Early stabilization often matters as much as the switch itself.
Cutover plan and ownership
Ownership clarity often reduces downtime risk more than additional technical complexity, since ambiguous responsibility can delay decisions during a high-stakes transition. Timing often tracks business calendars that limit finance and customer success disruption. Fast checks typically emphasize billing-correctness signals and platform stability indicators rather than broad feature validation.
Rollback and early stabilization
Rollback readiness depends on pre-agreed triggers tied to correctness and stability rather than subjective confidence. Early stabilization generally centers on heightened monitoring for replication lag, error spikes, and reconciliation drift as production traffic normalizes. Commercial exposure remains highest until billing and reporting outputs show sustained parity against defined thresholds.
