Self-Serve Analytics for B2B SaaS: A Data Engineering Reference Architecture for Customer-Facing Dashboards (Row-Level Security, Cost Control, and SLAs)
2026-05-06
Set requirements for secure, scalable customer dashboards
Self-serve analytics for B2B SaaS tends to become a product commitment rather than a reporting feature. Executive teams often encounter the same early tension: customer-facing dashboards must feel intuitive and responsive, while the underlying platform is still held to enterprise expectations around privacy, auditability, and predictable performance. The differentiator is rarely the embedded BI surface; it is the specificity of requirements across tenant isolation, data freshness, and reliability. When those expectations stay implicit, analytics demand commonly outpaces governance, and the gap shows up as access risk, cost variance, and missed expectations during enterprise evaluations.
Must-haves: privacy, predictable spend, and uptime
Enterprise buyers typically treat analytics privacy as non-negotiable and increasingly expect the control to be demonstrable. Predictable spend matters for the vendor as much as the customer, because embedded usage shifts warehouse cost from an internal team budget to a product P&L constraint. Uptime expectations also tend to become contractual, and availability targets without matching freshness and latency definitions often create interpretation gaps and escalation cycles.
Decide what to build vs buy
Embedded analytics introduces ownership boundaries across identity, authorization context, metric definitions, and the dashboard experience. Speed-to-market often favors packaged embedded BI, while control questions typically surface around RLS guarantees, semantic consistency, and performance governance. In many SaaS analytics programs, the more durable decisions center on where differentiation and assurance matter—consistent metrics, tenant isolation confidence, and operational reliability—rather than interface polish alone.
Choose a simple platform layout for embedded analytics
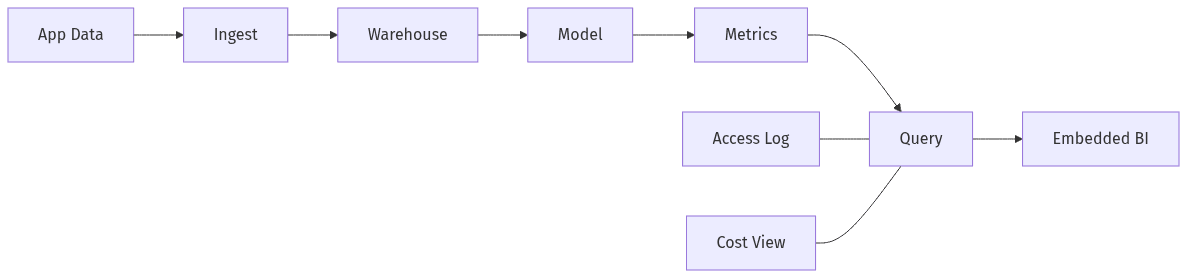 Simple layout for embedded customer dashboards
Simple layout for embedded customer dashboards
A reference architecture for customer-facing dashboards in B2B SaaS typically resolves into a small set of layers: ingestion from production systems, modeling into analysis-ready structures, a semantic or metrics layer for consistent definitions, and a serving layer consumed by embedded BI. Governance and monitoring span these layers because cost, reliability, and access assurance are cross-cutting constraints. Vendor choices such as Snowflake, BigQuery, or Databricks shape execution details, but multi-tenant realities remain similar: interactive queries are spiky, concurrency can surge, and tenant isolation must hold under load and platform change.
Organize data so metrics stay consistent
Metric drift becomes visible fastest in embedded analytics, because customers reconcile dashboards against invoices, exports, and internal reporting. Tenant keys and authorization context usually need to be first-class modeling concerns, not incidental columns, because they affect correctness and access control at the same time. Semantic layers reduce fragmentation by centralizing metric logic and versioning, which lowers the likelihood that product teams and customer-facing teams present conflicting numbers to enterprise stakeholders.
Protect customer data with strong tenant isolation
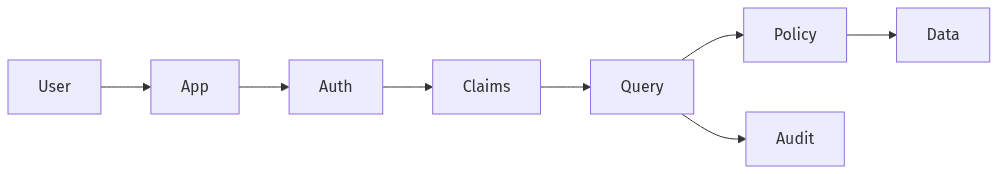 Tenant isolation checks across access path
Tenant isolation checks across access path
Tenant isolation sits at the center of trust for multi-tenant analytics, and row-level security is often the primary control surface for shared warehouses. The operational constraint is that embedded dashboards multiply access paths: interactive exploration, exports, API-driven queries, and background refreshes can all reach the same datasets. A recurring pattern in legacy embedded setups is treating BI-only RLS as sufficient, even though stronger assurance usually comes from isolation that remains valid regardless of the visualization tool. The executive risk is asymmetric: a single cross-tenant exposure can outweigh years of delivered product value and can stall enterprise evaluations.
Pick where access rules are enforced
RLS enforcement can sit in different layers, and that placement affects the strength of guarantees as well as operational overhead. Least-privilege principles generally favor enforcement close to the data, where policy applies across tools and query entry points. Enforcement primarily at the BI layer can reduce initial engineering effort, yet it increases dependence on consistent configuration and can widen the blast radius of misconfiguration or bypass through alternate access methods.
Make access reviewable and provable
Enterprise readiness typically includes the ability to produce evidence of who accessed which data and why access was permitted. Reviewability matters because authorization context changes over time—roles shift, customers churn, and entitlements evolve. Compliance references such as SOC 2 and ISO 27001 raise the bar for audit-friendly access records, since customer security teams often look for verifiable least privilege rather than assurances.
Control analytics spend without hurting the experience
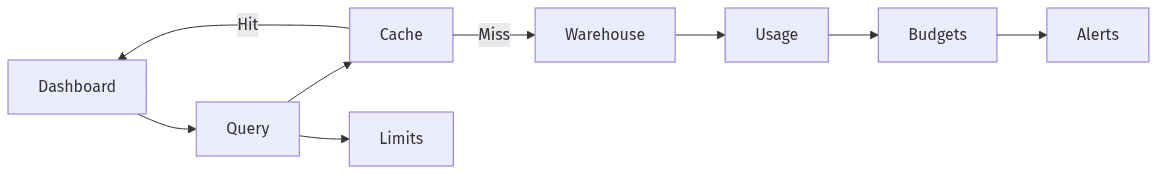 Cost guardrails with caching, limits, and attribution
Cost guardrails with caching, limits, and attribution
Embedded analytics changes the economics of querying: warehouse costs become coupled to customer behavior, and open-ended exploration can translate into volatile consumption. Spiky concurrency and repeated dashboard refreshes commonly create cost patterns that are hard to forecast using internal BI assumptions. Cost-to-serve becomes a product metric, particularly when analytics usage correlates with plan tiering, renewals, and support load. The underlying goal is cost stability that preserves an acceptable dashboard experience while preventing usage outliers from distorting margins.
Keep common queries affordable
Embedded usage often concentrates around a small set of top dashboards, creating a repeatable cost surface. Repeated work frequently comes from overly granular queries, dashboard designs that trigger many similar requests, and patterns that resemble N+1 query behavior at the analytics layer. Cost stability tends to improve when common queries rely on reusable, cache-friendly, aggregation-aware data shapes.
Prevent noisy neighbors and allocate spend fairly
Multi-tenant platforms routinely experience noisy-neighbor effects, where a single tenant’s exploration or concurrency degrades performance for others and inflates shared warehouse spend. Per-tenant attribution clarifies which customers drive consumption and supports defensible showback or chargeback conversations. Budgets, quotas, and alerts typically move cost and performance from surprise to managed variance, which matters when enterprise SLAs depend on stable capacity.
Plan reliability and rollout for enterprise readiness
Customer-facing analytics inherits expectations usually reserved for core application functions: contractual availability, defined latency tolerance, and transparency during incidents. SLO/SLA language provides a structured way to communicate those commitments, and error budgets translate reliability into measurable tolerance rather than aspirational statements. Freshness becomes equally productized, since customers treat dashboards as operational truth even when pipelines lag. A phased rollout approach tends to reduce reputational exposure, because early production usage surfaces real concurrency, query shapes, and support load that synthetic testing often misses.
Set freshness and availability expectations
Dashboards rarely share the same freshness requirement, and tiered freshness is a common pattern that balances customer value against platform cost and operational overhead. Availability targets carry more weight when paired with measurable SLIs and defined exceptions, rather than vague “always up” assumptions. Per-dashboard definitions for freshness and latency reduce ambiguity and support error-budget trade-offs when reliability pressure collides with warehouse spend.
Roll out in phases with a readiness check
Enterprise analytics maturity typically progresses from embedded visualizations toward a governed analytics product with explicit commitments and auditable evidence. Early phases often concentrate on essential dashboards and hardened tenant isolation, while later phases shift toward broader self-serve exploration, reliability instrumentation, and cost governance. Readiness gates become politically consequential when enterprise sales cycles depend on security reviews, since assurances without operational evidence often extend evaluation timelines.
