Zero-Downtime Laravel/Rails-to-React Frontend Modernization for B2B SaaS: A Strangler-Fig Migration Plan with Feature Flags
2026-04-29
Decide if an incremental approach fits your SaaS goals
Incremental React frontend modernization often fits B2B SaaS teams when uptime expectations and revenue sensitivity make a big-bang rewrite commercially difficult to justify. The strangler-fig migration pattern frames modernization as controlled substitution rather than wholesale replacement, which supports roadmap continuity under constrained engineering capacity. Executive scrutiny typically focuses on risk controls, explicit success criteria, and whether hybrid operation stays stable long enough to justify UX change. Uncertainty usually clusters around routing coexistence, session continuity, and regression exposure—not around React itself.
Readiness and risk check
Readiness discussions typically surface constraints that are easy to underestimate in planning: session and cookie scope, CSRF expectations, legacy route collisions, and the practical limits of test coverage in a hybrid app. Exit criteria often matter as much as entry criteria, because prolonged dual-state complexity becomes an ongoing operational cost. The highest-consequence risks concentrate where authentication, navigation, and revenue-critical paths intersect.
Simple phased rollout plan
Phasing commonly separates foundation work from visible UI change, followed by a pilot that validates side-by-side stability, and then a scale-out phase that replaces screens by priority. That sequencing reflects a recurring delivery constraint: early value depends less on the volume of migrated pages and more on confidence that rollout controls, shared authentication, and routing conventions stay predictable under production load.
Keep navigation and key pages working during the transition
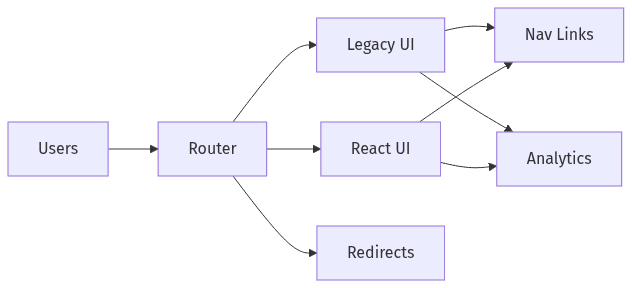 Hybrid routing splits traffic between legacy and React pages
Hybrid routing splits traffic between legacy and React pages
Navigation continuity often becomes the perceived downtime risk in zero-downtime React frontend modernization, because broken deep links, inconsistent redirects, and split navigation states show up as immediate customer friction. Hybrid routing choices—path-based routing, reverse-proxy segmentation, or embedded React islands inside server-rendered pages—carry different tradeoffs in URL stability, performance behavior, and operational governance. In B2B SaaS, sensitivity is usually highest around high-traffic application routes, bookmarked admin screens, and internally shared links used by support and sales.
Navigation approach and tradeoffs
Path-based routing tends to preserve bookmarks and user mental models, while embedded React islands reduce surface-area change but can prolong mixed rendering and ownership boundaries. Reverse-proxy separation can clarify boundaries but often introduces operational overhead and route governance friction. Across options, link preservation and predictable 404/redirect behavior are the main drivers of perceived stability.
SEO and analytics continuity
Analytics drift often appears during incremental adoption because page identity, route patterns, and client-side transitions change data collection assumptions. Search visibility becomes relevant for marketing surfaces and documentation-like pages, even when core application screens sit behind authentication. Consistency in URL structures, event naming, and attribution typically matters more than the rendering approach.
Avoid login friction across old and new experiences
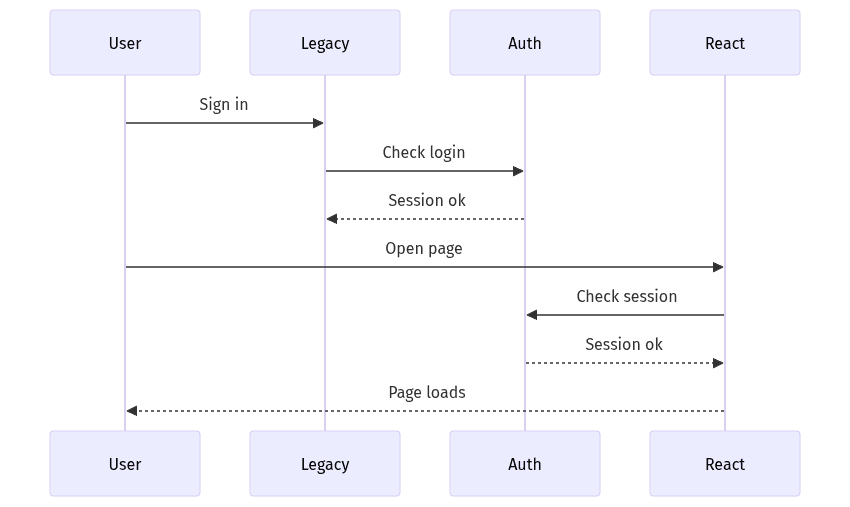 Shared session enables smooth handoff between old and React
Shared session enables smooth handoff between old and React
Login and session continuity often represent the sharpest edge of a Laravel/Rails-to-React transition, because users experience even minor breaks as trust erosion. Hybrid apps amplify the risk: old and new screens must agree on identity, session state, and authorization semantics while requests traverse different rendering layers. Misconceptions also appear here, particularly the assumption that JWTs are required for React, even when cookie-based sessions already match the product’s security and UX needs. For executive stakeholders, the central concern is uninterrupted access across a mixed UI estate.
Shared sign-in experience
Shared sign-in typically hinges on a single source of truth for authentication and a consistent session contract across server-rendered and React surfaces. Cookie sessions often remain workable in a hybrid model, provided cookie scope, same-site settings, and CSRF expectations remain aligned across both stacks. Misalignment usually surfaces as repeated logins, broken handoffs, and higher support volume.
Security basics to maintain trust
Security posture during UI modernization typically depends on preserving established controls, not on adopting a new authentication model for its own sake. OWASP-aligned expectations around session management, CSRF protections, and secure cookie policies remain relevant as screens move. Compliance-adjacent obligations such as SOC 2 evidence and cookie handling practices often become more visible when authentication and routing responsibilities span both legacy and new interfaces.
Release React changes safely with feature flags
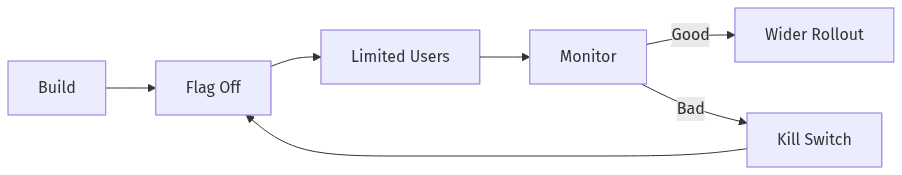 Feature flag rollout with monitoring and fast rollback
Feature flag rollout with monitoring and fast rollback
Feature flags often act as the commercial safety mechanism behind strangler-fig migrations, because they turn UI change into reversible exposure rather than permanent replacement. In B2B SaaS, progressive delivery aligns with customer segmentation, enterprise rollout coordination, and support readiness. The most valuable property is optionality: controlled targeting limits blast radius, while kill-switch behavior shortens time-to-recovery when regressions surface. Over time, unmanaged flags accumulate as operational and code-path debt, so lifecycle discipline commonly becomes part of the modernization risk narrative alongside routing and authentication.
Flagging strategy for safe rollout
Flagging approaches often resemble layered controls: user or account targeting for early exposure, percentage rollouts as confidence increases, and role-based segmentation for internal teams. Measurement expectations typically focus on adoption, error-rate movement, and latency shifts rather than “features shipped.” Cleanup discipline is often what separates controlled progressive delivery from long-lived entropy.
Rollback and monitoring readiness
Rollback credibility depends on observability that can attribute issues to a flagged React surface versus legacy pages. Error tracking, performance budgets, and clear SLO language often become executive shorthand for readiness. Kill-switch semantics matter most when the failure mode includes broken revenue workflows, authentication loops, or navigation issues that trigger immediate support pressure.
Prevent regressions with focused QA and monitoring
Regression risk increases during incremental React adoption because the product becomes a hybrid system with more interaction paths and more rendering permutations. B2B SaaS leaders often treat QA strategy as a proxy for delivery predictability: unreliable tests create release hesitation, while excessively broad E2E coverage tends to become slow and brittle. More stable delivery patterns usually correlate with selective, high-signal automation around critical flows and monitoring tuned to customer-impacting failures. In this context, “zero downtime” reflects operational control, not an absence of defects.
Hybrid testing for critical flows
Hybrid testing emphasis typically concentrates on revenue-adjacent journeys, authentication boundaries, and cross-surface navigation where legacy and React screens meet. E2E suites can provide confidence for top flows, while integration and contract tests reduce surprises at the seams between UI behavior and backend expectations. A common risk pattern is partial coverage that misses edge cases introduced by mixed routing and shared session state.
Operational readiness for uptime
Operational readiness usually shows up in observability depth and incident response clarity rather than in additional release ceremony. Monitoring that captures latency, error rate, and front-end performance regression signals serves as an early indicator of customer experience drift. When modernization overlaps active roadmap delivery, predictable release behavior and well-understood rollback paths often determine whether stakeholders view the migration as manageable or as a source of business risk.
